The technology and the new communication systems have allowed the jump from the traditional “telephone” to the new video door phones IP that become key elements for the control of access to a building with a high guarantee of security and efficiency. Digital systems bring many variants and possibilities to the electronic doorman. Long-distance communications, door opening using codes or proximity cards, and integration with other applications instead of being a separate device to create a truly efficient and secure access control system.
The doorman is an indispensable element in any building, whether it is a community of neighbors, institutions or companies since it is the primary mechanism of communication and security that is used to control the doors to the building.
An electronic Door Access Control System, in its most basic version, is a double – street door intercom, with the possibility of operating an automatic door that unlocks the lock and allows the door to be opened to allow passage into the interior.
New features are being added year after year, technology imposes itself on our life and makes it safer and simplifies access control tasks.
Applications for the Smartphone
We are united to our smartphones, and for that reason, the technology for the security uses this fact to adapt the doorman to the new ways to communicate and to operate.
The Mobile Phone for Receiving Calls From the Video Intercom
The door phone pairs with the mobile applications where you can view the images of the door intercom camera on the screen of a mobile device. Thus, you will always know who is in front of the door and will have the power to decide if you want to open to let the visitor enter.
The Mobile Phone as an Access Key
Applications that convert the mobile phone into a card that allows you to access a building. The application communicates with the intercoms via NFC and Bluetooth technology to identify the users.
Buying access control systems is one of the best way to safeguard goods, data, people and information. On the contrary to what many would believe, teams are easy to access and install for individuals, as well as profitable and suitable for businesses.
Wondering How An Access Control System is Connected To Everyday Life?
- Door Access Control System: You can leave access only on a particular niche for a defined user, for example, the housekeeper. This configuration will be done by programming your keypad which allows activating codes on a predefined time range.
- Temporary opening: from a distance, you can open the door to the plumber who comes to make the repairs. This configuration is feasible, for example, by creating a temporary code on your keyboard that you will provide to your craftsman.
- History: you know precisely at what time the door was opened and by whom. Convenient to monitor that children are well back from school.
- Scenario: You can integrate the opening of the door into a scenario so that the alarm is deactivated as soon as you open your door.
Home Automation in Hotels is No Longer A “Must” But Merely A “Standard”!
Talk about what you could do and achieve with home automation in hotels is quite difficult because there is no limit to achieving integration of all plant systems supplied to the hotel. The entire control system is easily manageable with a click of a computer station at the reception or even from a tablet or a smartphone with a simple touch that allows us to have an eye on the status of the hotel and customers before the receptionist.
The integrated automation systems dedicated to hotels and accommodation facilities allow a double benefit for those who work in these areas:
- Optimize the work, making it more effective, efficient and safe, saving on operating costs and the activity of those linked to consumption.
- Make it a comfortable customer lounge, offering an innovative service and is sure to charm.
- The entire management of rooms and public areas such as reception, restaurant, elevators, can be controlled by the staff of the facility, through any control interface, such as the central desk of the lobby. Similarly, customers can use tablets, remote controls, push buttons or touchscreen to communicate with their room or reception.
What Solutions To Manage Access?
The Most Commonly used Materials are:
1:- The coded keypad (for example, the digicode): it replaces the key with a stored code which transmits an opening command to the electric lock, or an electric strike. An electric strike makes it possible to electrify a mechanical lock without modifying it. Its installation is simple: an electrical connection is necessary, as well as the replacement of the back plate located on the door jamb.
2:- The audio gatekeeper: similar to the encrypted keypad, it also allows access to a third party via a voice connection via a telephone line, radio frequency or power line transmission (intercom) and of a remote opening command.
3:- The video door entry system: identical to the audio gatekeeper, it also allows the transmission of the image of the person requesting access. The occupant can also communicate with the visitor and open (or not) his door at a distance, to a delivery man or a housekeeper for example. This system operates with a door release button or an electric strike.
This hardware can have a time management, allowing a virtually free access (a simple press of a button to obtain access). They are mostly treated as “anti-vandal” and some work with badges instead of a key or stored code.
1:- The video: it is booming. A camera can be integrated into the Detector of individual alarm systems. A series of photos or a film are made during the intrusion attempt and can be received remotely on a smartphone via a transmitter to give the alert. Security cameras with facial recognition are also beginning to develop (photo below). They learn to recognize faces and identify the people they see entering the dwelling. If this is an unknown, the owner is alerted to his smartphone and can immediately notify the police.
2:- The electronic locks: Finished searching for lost keys at the bottom of the handbag. They work with different wireless communication modes (Wi-Fi, Bluetooth, NFC, radiofrequency) and facilitate everyday life: opening and closing the door remotely by smartphone; access is given to selected person in the absence of keys, etc.
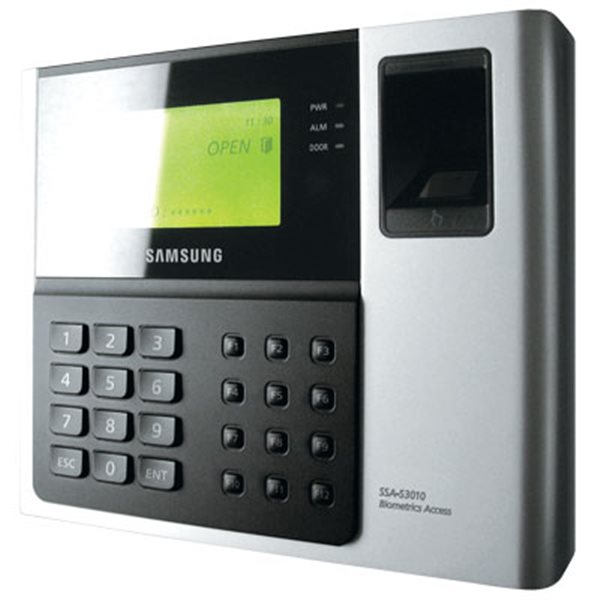
3:- The Fingerprint Access Control System also makes its appearance: It allows entering the housing by putting the finger on a Sensor. The fingerprints of the occupants are recorded beforehand. Permission to access certain hours can also be given to third parties.